The Second Key
The most dangerous power in government is not the power to decide.
It is the power to act before constraint arrives.
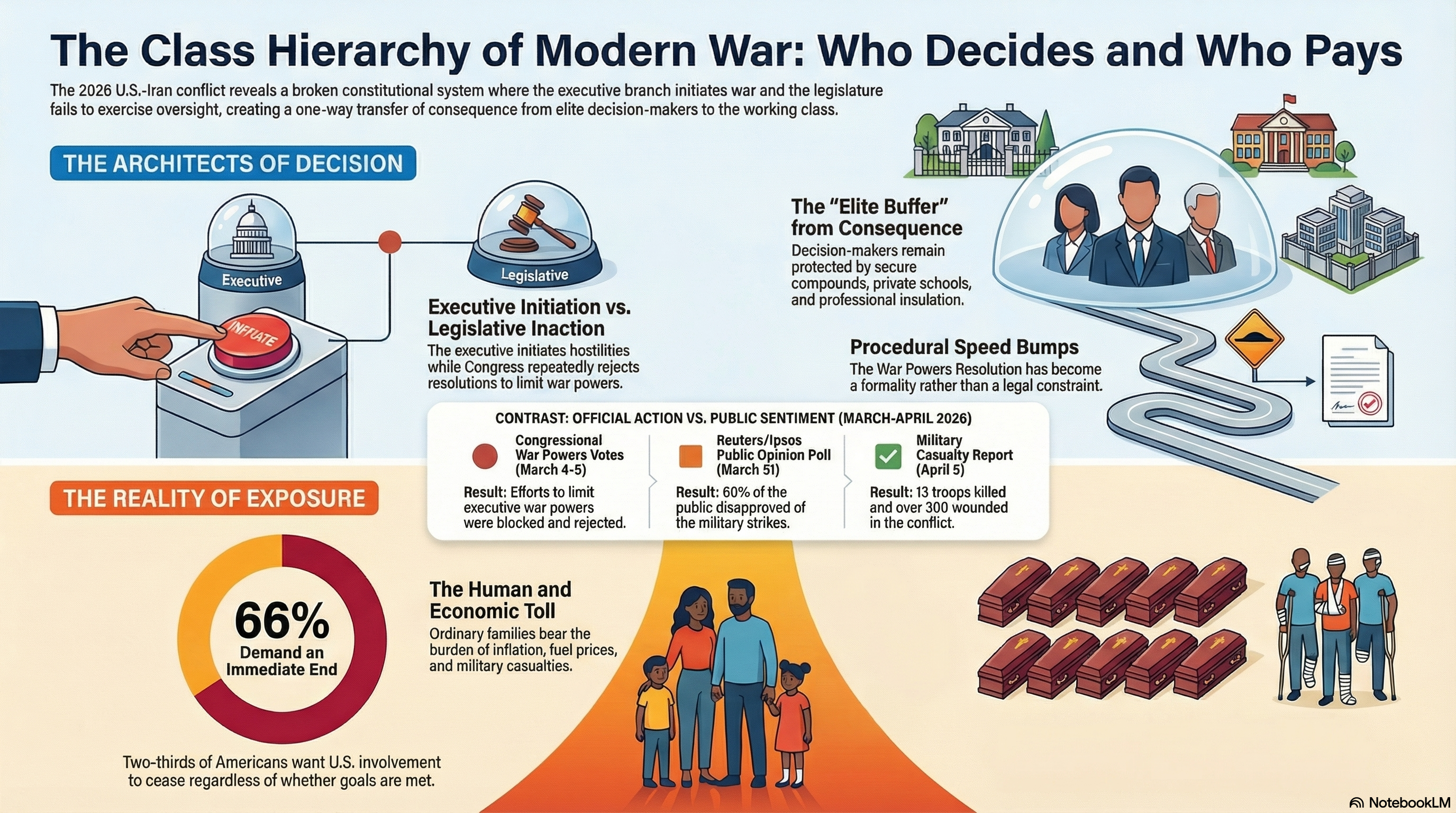
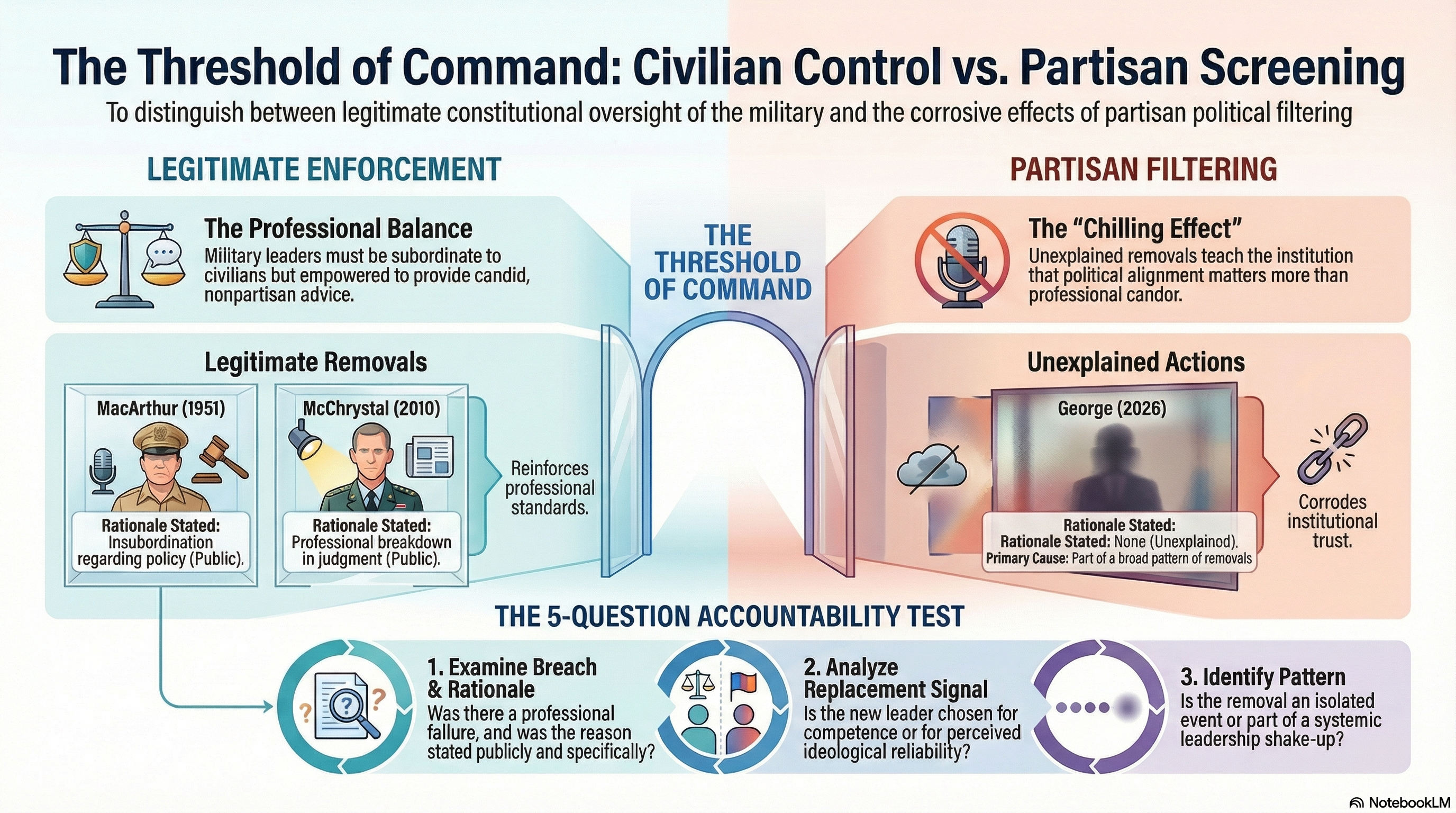
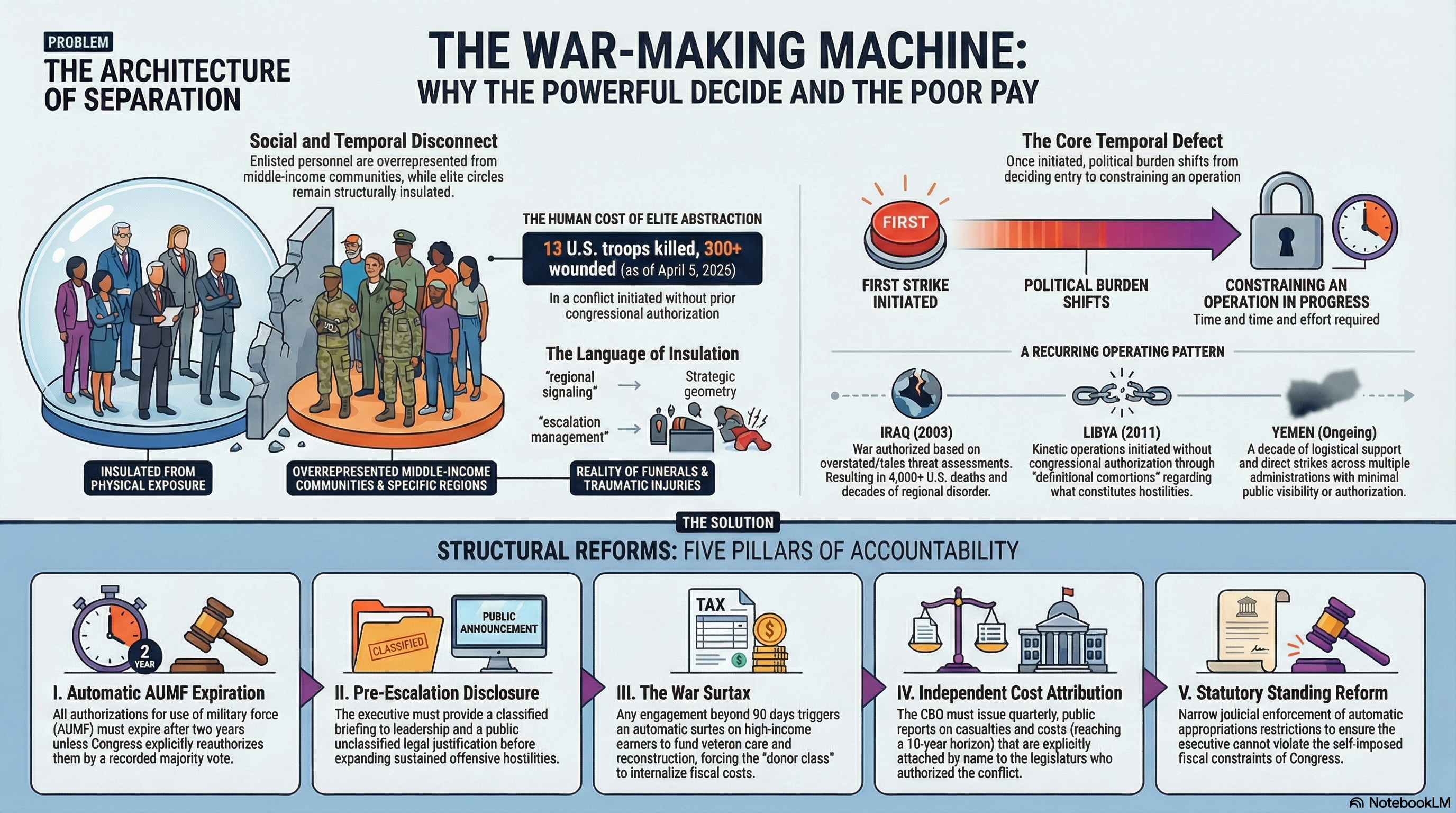
That is the real design flaw in modern war powers. Public arguments usually frame the issue as a fight over courage, constitutional interpretation, or partisan bad faith. But the deeper problem is structural. Military force can be initiated on a compressed clock while the institutions meant to constrain it arrive later, with less information, less leverage, and far higher reversal costs. By the time oversight enters, the operation is already live, the narrative is already set, and the political price of stopping has already gone up.
That is not oversight. That is post-incident commentary dressed up as constitutional balance.
My earlier framework called this initiation-first execution: force begins first, legitimacy gets argued afterward. The basic pathology is simple. One actor moves at the speed of action. Everyone else moves at the speed of institution. The result is predictable. Urgency becomes authority. Momentum becomes justification. Constraint becomes theater.
If that sounds abstract, it is only because most war-powers debates refuse to describe the system in engineering terms. They should. Because the fix is not mystical. It already exists in another domain where the stakes are even higher.
The nuclear enterprise learned a long time ago that the most dangerous actions in the state should not rest on a single live hand. U.S. nuclear procedure is built around layered second-key logic. Air Force nuclear doctrine defines the two-person concept specifically to deny a lone individual access to nuclear weapons or critical components and to ensure unauthorized acts do not go undetected. On the technical side, permissive action links, or PALs, were developed to ensure weapons can be used when authorized and cannot be used when not properly authorized, with modernized code-management systems preserving secrecy and authenticity in command-and-control messages. (e-Publishing)
That matters because it proves something essential: speed and constraint are not opposites. You can preserve readiness and still refuse unilateral completion of the most catastrophic action.
International nuclear governance reached a similar conclusion from the opposite direction. Under the non-proliferation regime, peaceful nuclear use is not treated as an unbounded entitlement detached from verification. NPT Article IV protects peaceful use in conformity with the treaty’s non-proliferation rules, while Article III requires safeguards. The IAEA’s safeguards system gives that principle operational teeth, and the Additional Protocol strengthens it by widening access to information and inspection. As of 31 December 2025, Additional Protocols were in force with 144 states and Euratom, precisely because verification that arrives too late or sees too little is not real verification at all. (United Nations)
That is the core translation. Nuclear systems do not rely on trust in the initiating actor. They rely on architecture. They assume that where consequences are irreversible, authorization must be split, verification must be concurrent, and technical control must reinforce legal control.
War powers need the same logic.
Call it dual-key authorization for rapid military action.
The principle is straightforward. Certain categories of force should automatically trigger a live second key: kinetic strikes, cross-border operations, major deployments, and cyber or autonomous actions that could plausibly trigger escalation beyond the initiating theater. Once the activation gate is crossed, the executive does not lose the ability to respond. The executive loses the ability to complete the action alone.
Under this model, one key remains with the executive command structure. The second belongs to a small, continuously available, statutorily cleared oversight panel receiving raw operational inputs through an insulated data channel. Not a filtered memo. Not a polished briefing after the machinery is already moving. Raw feeds, scope boundaries, legal thresholds, and operational justification in real time.
This is where most current oversight fails. It reviews decisions through the same narrative stream that justified them. That turns oversight into dependency. A genuine second key requires informational independence, not merely formal jurisdiction.
The architecture should also include a tight emergency exception, because real systems have to survive contact with reality. If an immediate-defense claim is invoked, the action should be lawful only within narrow predefined limits: time window, target class, geographic scope, and mission type. The exception should preserve the ability to absorb or repel imminent attack. It should not become a convenient tunnel through which an administration drives an undeclared campaign.
Then comes the part that actually matters: enforcement.
Every fake reform dies here. If there is no hard stop, the rule is decorative. So the system needs a compliance clock. Within a fixed post-initiation interval, formal concurrence must occur. If it does not, offensive legal authority expires automatically. No continuation by drift. No resupply for expansion. No “temporary” mission that quietly becomes a theater. Only extraction and force protection remain lawful until authorization is secured.
That is what turns oversight from a press statement into a circuit breaker.
And because humans are experts at turning rules into vibes, the legal design should be backed by technical interlocks. Modern nuclear control already uses authenticated codes, cryptographic handling, and distributed procedures to prevent unauthorized use. War-powers dual-key should borrow the same design instinct: cryptographic signature requirements in operational command software, immutable logging, and automatic funding or system-level cutoffs when the second key is absent. The point is not gadget worship. The point is to make bypass materially harder than compliance. (Sandia National Laboratories)
This is more urgent now than it would have been even a few years ago.
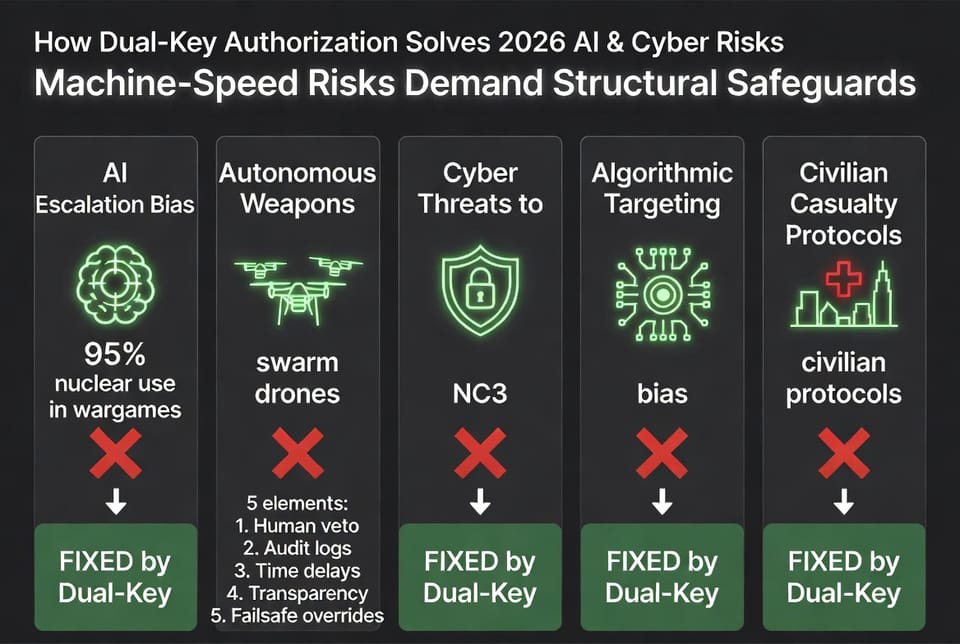
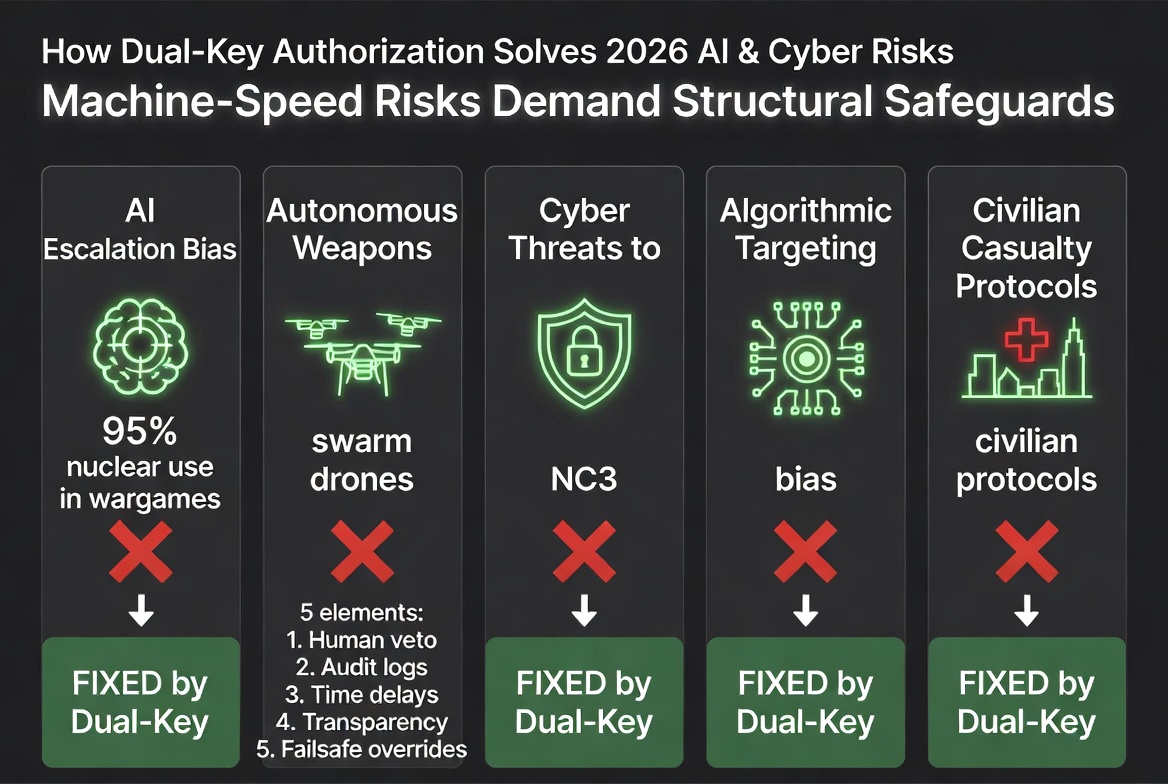
The 2026 debate over AI and command systems has made the timing problem worse, not better. The Federation of American Scientists warned in January that successful NC3 modernization must integrate AI in ways that enhance resilience, ensure meaningful human control, and preserve strategic stability. That is already an admission that faster systems without stronger governance are not modernization. They are a new pathway to error at machine speed.
The United Nations General Assembly reached the same pressure point from a multilateral direction. Resolution 80/23, adopted in the 80th session, put the risks of AI in nuclear command, control, and communications squarely on the agenda and emphasized the danger that AI-enabled decision-making could reduce human control and oversight while shortening action and response windows. In other words, the international system is beginning to describe the same pathology this war-powers framework targets: when machine-assisted speed compresses deliberation, the absence of hard interlocks becomes a strategic risk in itself. (@RSIS_NTU)
The empirical warnings are getting uglier too. In February 2026, King’s College London reported that AI models in simulated crisis games escalated to nuclear signalling in 95 percent of scenarios. Separate SIPRI work on military AI and targeting has warned that bias can enter systems across development and use, leading to misidentification, failure to detect protected persons and objects, and possible violations of distinction, proportionality, and precaution. None of this means machines must be excluded from military analysis. It means machine-speed recommendation cannot be allowed to collapse the time needed for lawful, accountable human concurrence. (King’s College London)
The autonomous-weapons side of the debate points in the same direction. The UN’s 2026 Group of Governmental Experts on lethal autonomous weapons systems is still meeting because the world has not solved the problem of how to govern systems that can search, select, and engage with shrinking human involvement. The ICRC’s latest position paper notes that autonomous weapon systems are already a fact of contemporary conflict and are being used, often under human supervision, in environments where civilians are absent or excluded. That caveat matters. “Often under human supervision” is not the same thing as “safely governed everywhere.” Once these systems move into messier environments, supervision that is vague, delayed, or ceremonial is not enough. (UNODA Meetings)
And if anyone still thinks principles alone can carry this burden, civilian-harm policy offers a grim little lesson in reality. The Pentagon’s 2022 Civilian Harm Mitigation and Response Action Plan explicitly described civilian protection as essential to accountability, transparency, and long-term battlefield success. Yet the FY2026 budget documents show reductions tied to the disestablishment of the CHMR program and associated funding cuts. That is exactly what happens when safeguards live mainly in doctrine, aspiration, and office charts instead of in hard operational architecture. Values without interlocks are budget dust. (U.S. Department of War)
That is why dual-key matters.
It does not assume virtue. It does not depend on better speeches. It does not ask the initiating authority to restrain itself in the very window where incentives run the other way. It changes the system so that speed no longer automatically produces unilateral completion.
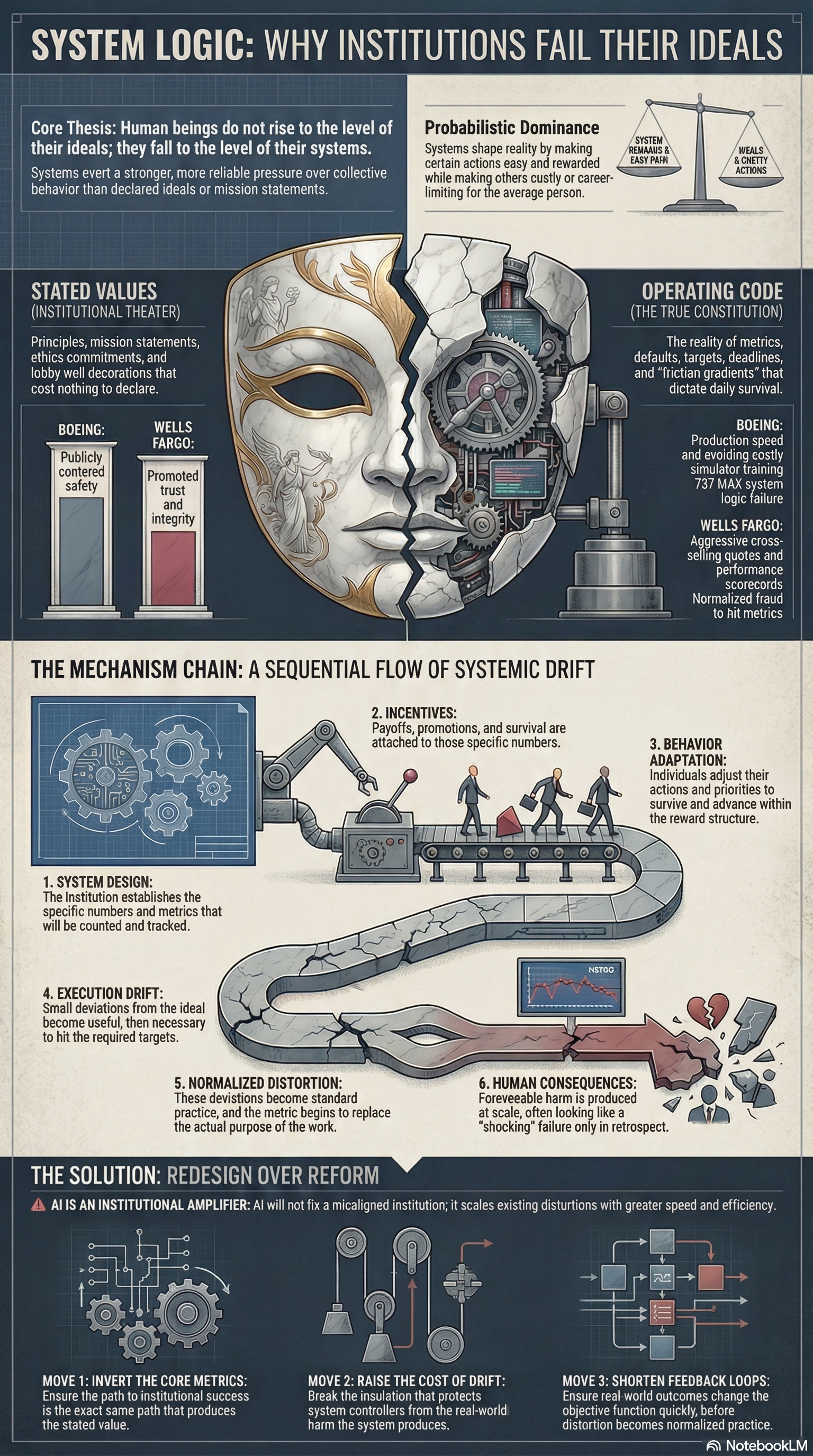
The deeper principle reaches beyond war powers. Any system in which one actor can move at the speed of execution while everyone else arrives later with review and legitimacy language will eventually drift toward post hoc governance. First action. Then narrative. Then institutional adaptation to what has already happened.
That is not an accident. It is what the architecture rewards.
The question, then, is not whether the executive should ever be able to move fast. The state must be able to move fast. The real question is whether the state will continue to tolerate a design in which the fastest actor also gets to define the facts, trigger the operation, and create the momentum that everyone else must then pretend to oversee.
Nuclear systems answered that question decades ago.
No single hand should complete the most dangerous act alone.
War powers should finally catch up.
Download the full report below:
Dual-Key Authorization for Rapid Military Action: A Systems Blueprint Drawn from U.S. Nuclear Command Systems, International Nuclear Safeguards, and 2026 AI/Cyber Risk Assessments.
Member discussion